As part of a standardization project, we have been enabling new port-security options on our Access switches that provide connectivity for end-users. When we made this change for a switch that serves around 240 users, we started to receive alerts for port security violations from three hosts at very inconsistent hours. Below is a small sample of one of the broadcast storms.
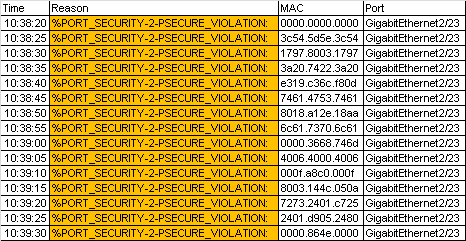
Given the large amount of MAC addresses that were broadcast in a short amount of time, the switchport port-security maximum 50 was being triggered after the switch saw the 51st MAC address.
interface GigabitEthernet1/1
description Access Port
switchport access vlan 200
switchport mode access
switchport port-security maximum 50
switchport port-security
switchport port-security aging time 1
switchport port-security violation restrict
no logging event link-status
storm-control broadcast level 3.40
storm-control action trap
spanning-tree portfast
ip dhcp snooping limit rate 50
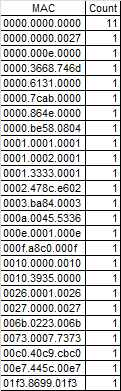
I consolidated all the MAC addresses seen into a table and was not able to find any duplicates. A search on a OIU database also showed that they were unregistered so they appeared to be randomly generated.
Looking at the MAC address-table for each port after the storm incident, I discovered that each port contained only a single Dell computer with a Intel 82579M Gigabit NIC. Some research lead me to a case of OptiPlex 790, 7010, 9010 and Latitude E6520/E6530 systems generating a network broadcast storm after coming out of sleep mode (2) and requiring a driver update on the Intel NIC in order to fix the issue.
References
- http://forums.juniper.net/t5/Ethernet-Switching/Power-saving-NICs-Dell-causing-EX3300-VC-port-problems/td-p/182897
- https://supportforums.cisco.com/discussion/11141666/port-secuity-issue-win-7
- http://www.dell.com/support/troubleshooting/bz/en/bzdhs1/KCS/KcsArticles/ArticleView?c=bz&l=en&s=dhs&docid=615706
- http://www.networksteve.com/windows/topic.php/Vista_Sleep_Mode_and_MAC_addresses/?TopicId=25326&Posts=1